
You're presented with traffic capture files which contain downloaded files. You need to examine those files, analyze them and extract the downloaded files from the PCAP file.
\nThe first PCAP file can be found at Desktop/Module7/Lab20/FileCarving.s0i0.pcap.\nLeverage Wireshark's statistics to determine which protocol the file downloaded? Also, report through what domain was the file downloaded.
\nRecall how each format has a unique header which can be used to identify that file, using this knowledge you can identify the specific streams that were generated during the downloading of the file. Once you identify those streams, extract the downloaded file from within them, using Wireshark.
\nArmed with the knowledge you acquired on tasks 1 and 2, examine the second PCAP file and try to extract the downloaded file from it.
\nYou can find the second PCAP file at Desktop/Module7/Lab20/file2.pcap
", "published_date": "2020-10-20T15:32:26Z", "solutions": "# Solutions\n\n## Task 1: IDENTIFY THE PROTOCOL AND THE DOMAIN THROUGH WHICH THE FILE WAS DOWNLOADED USING WIRESHARK\n\nAs usual, start by taking a look at the file's statistics is always a good place to begin.\n\n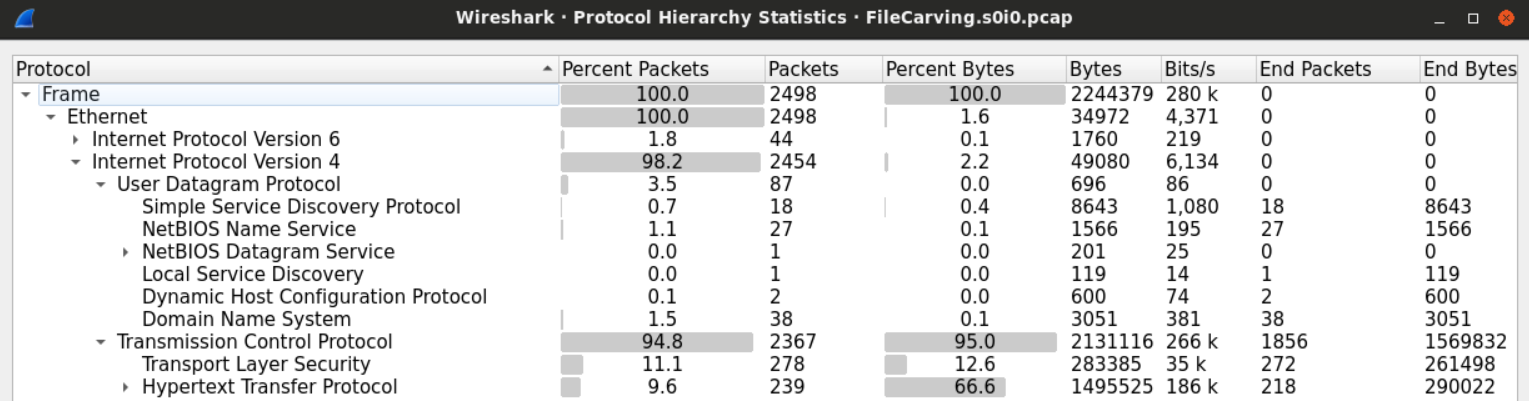\n\nFrom the protocol hierarchy figure, it seems that HTTP is the protocol which the file we're looking for was downloaded through.\n\nIt may be a good idea to look at the HTTP requests made.\n\n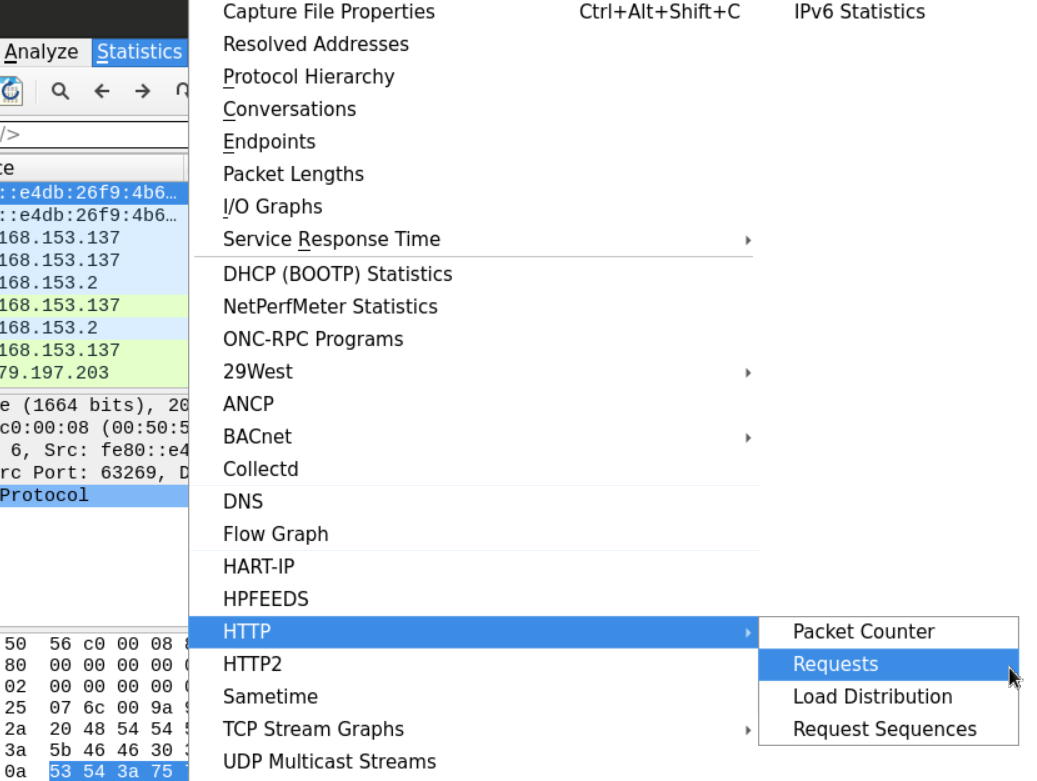\n\nExamining the requests made can help us know what type of file we're looking for.\n\n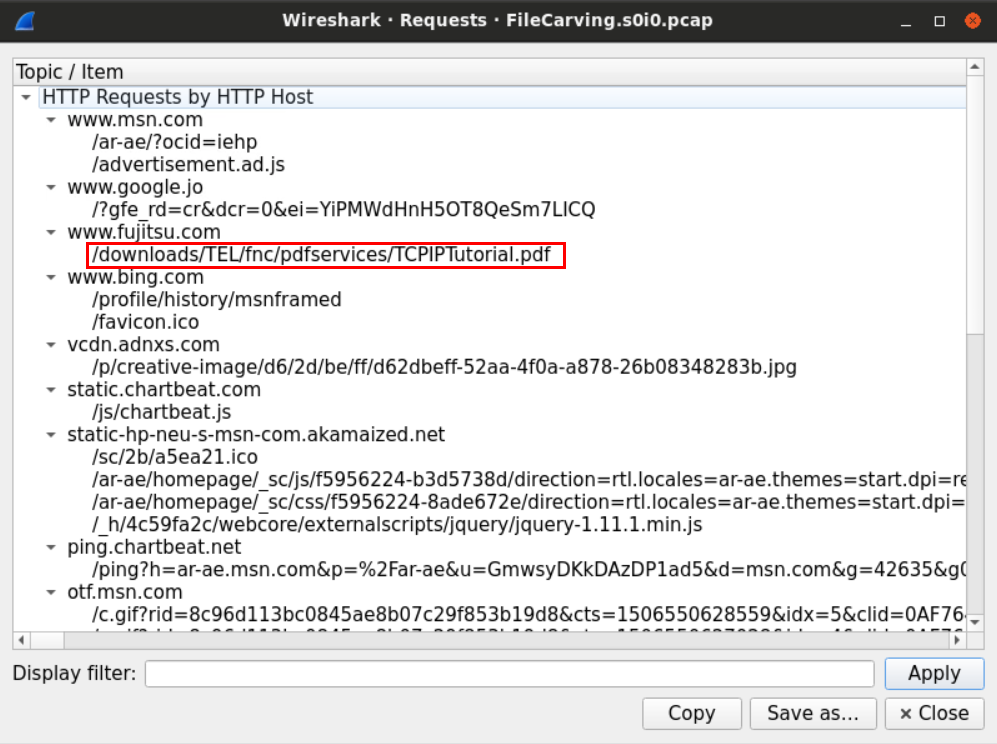\n\nNow we know that it is a PDF file.\n\n## Task 2: EXTRACT THE DOWNLOADED FILE USING WIRESHARK\n\nTo extract the downloaded file, we need to find the network streams which contain that file and extract those bytes into an independent file to open later.\n\nOne way to look for the file is using its magic number. Recall how each format has a unique header that can be used to identify that file.\n\nWe know from the previous example that the user has downloaded a PDF file from the BBC website using HTTP protocol.\n\nWe can use that knowledge to our advantage and look for the PDF signature within the PDF HTTP stream. Using the filter `http contains \"PDF\"`.\n\n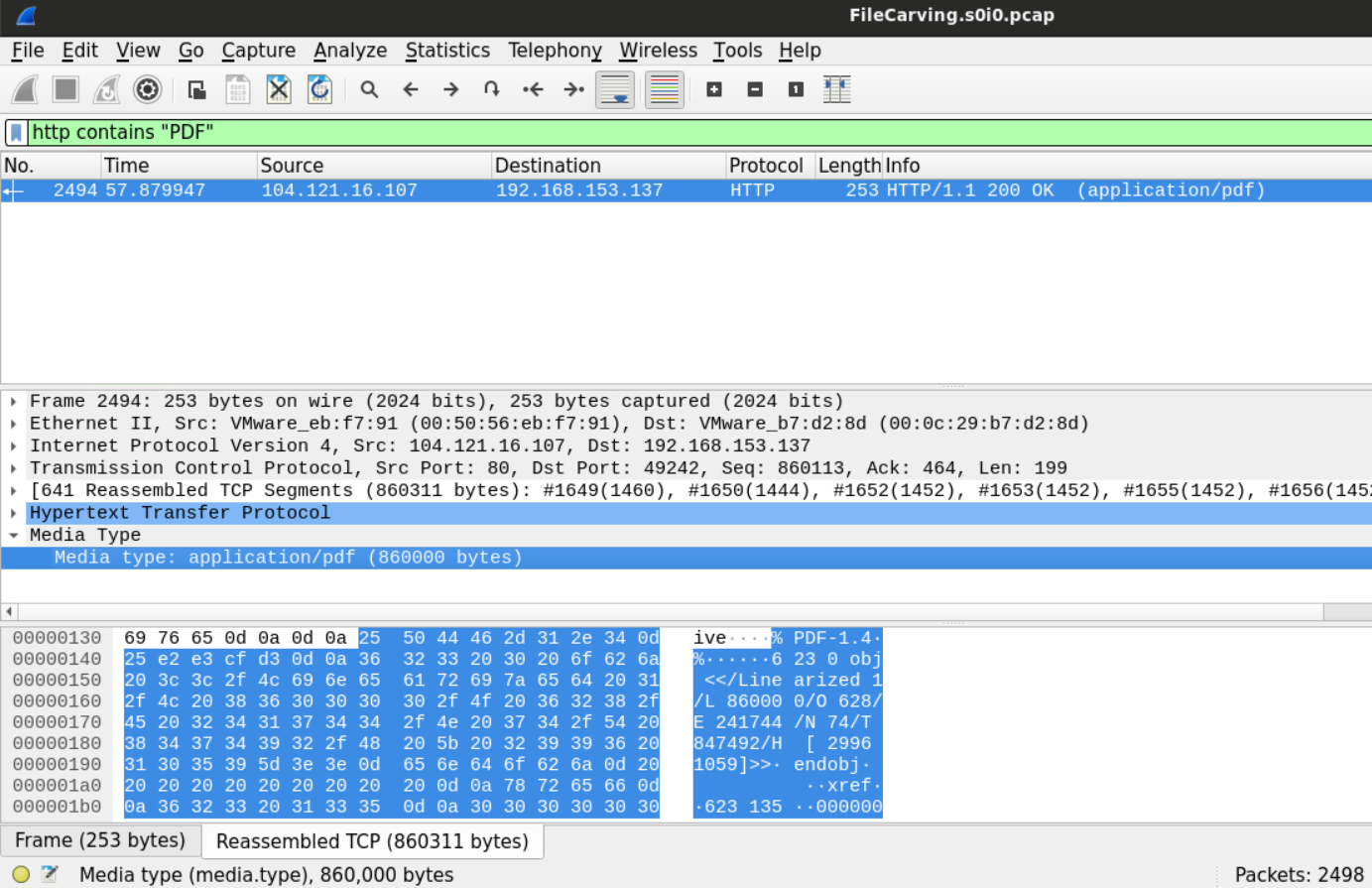\n\nAfter we've found the file and highlighted its bytes, we can use the Wireshark extraction feature to dump those bytes into a separate unique file.\n\n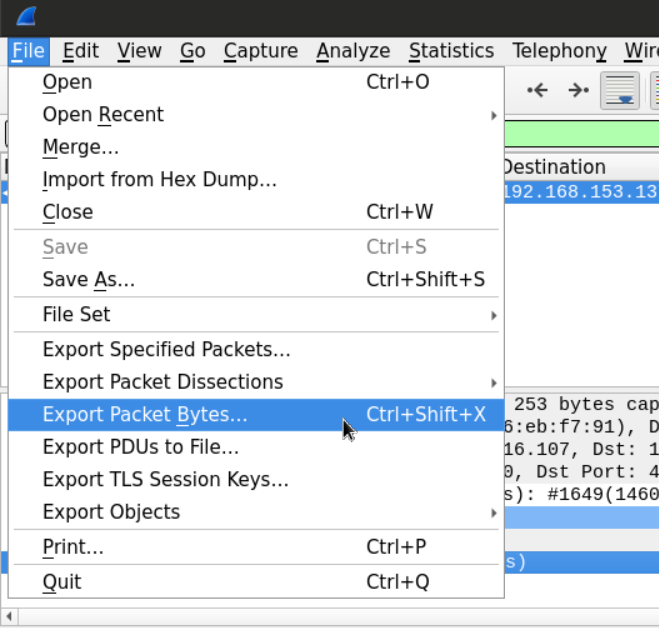\n\nThe new file will be saved as a .bin file, all we need to do is to change the extension and open the file with a PDF reader.\n\n\n\nAnother way to do this would be to export all the objects downloaded through HTTP.\n\n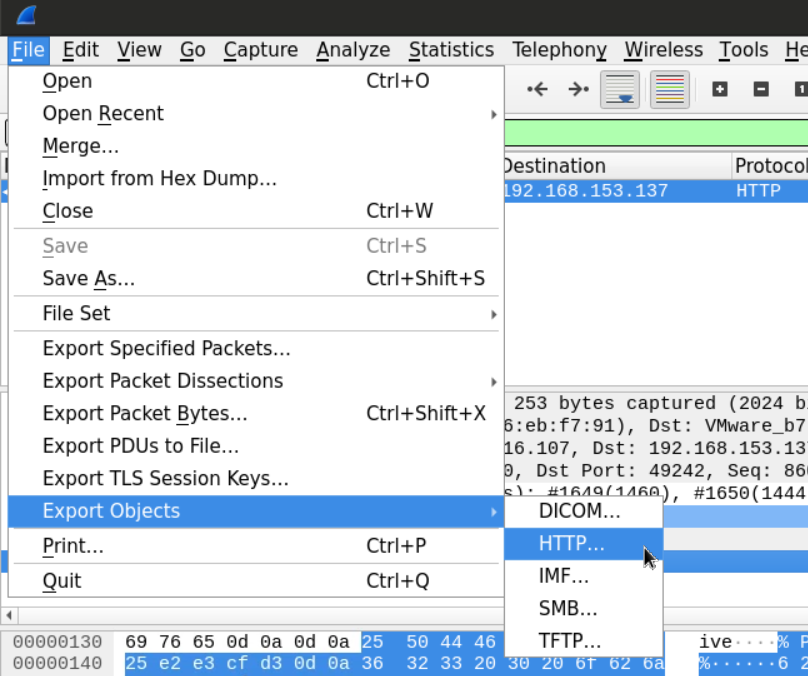\n\nThis will give us the list of the objects which we can pick from\n\n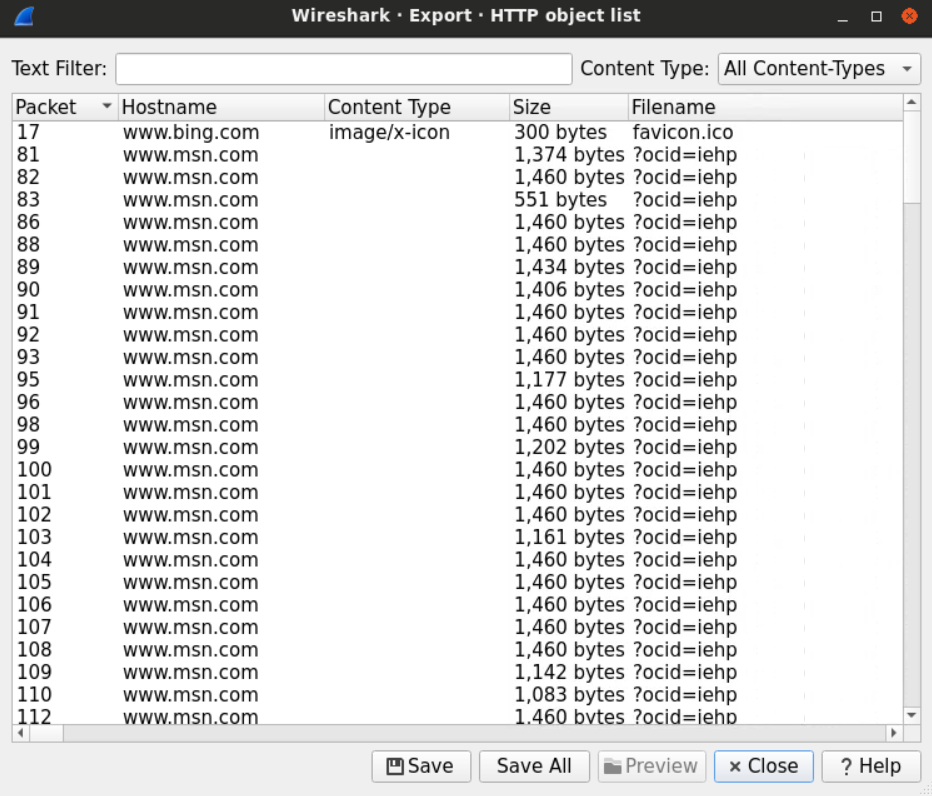\n\nAfter sorting the files at the destination folder, we can examine the extensions and open the files that look interesting to us.\n\n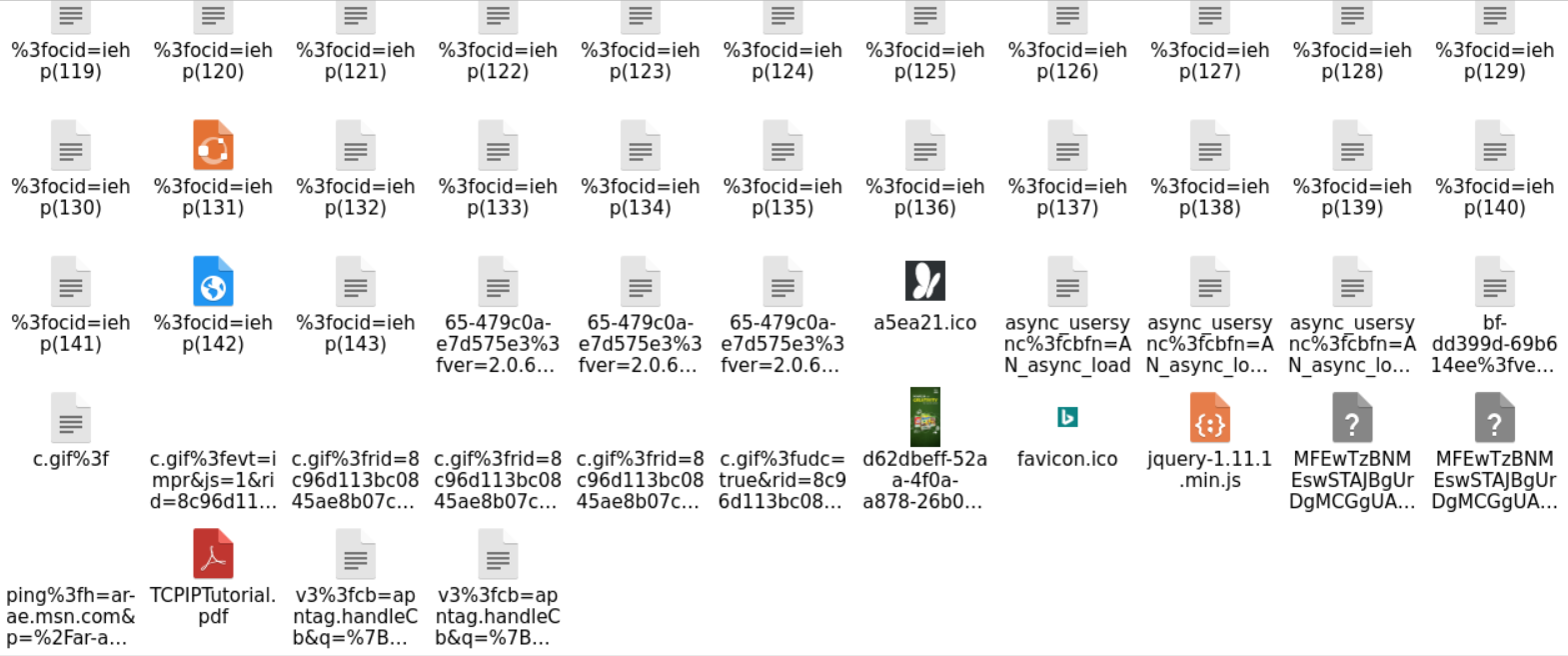\n\n## Task 3: EXAMINE THE SECOND FILE AND TRY TO EXTRACT THE DOWNLOADED FILE FROM IT\n\nFirst, let's load the PCAP file located at **Desktop/Module7/Lab20/file2.pcap** on Wireshark.\n\nThe protocol hierarchy for this cap file looks a little different than the other files we examined.\n\n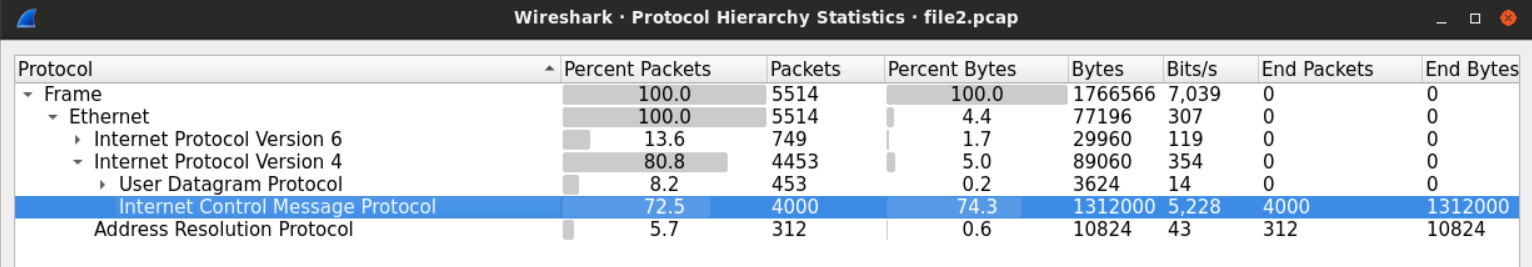\n\nThe amount of ICMP traffic within the file is more than normal.\n\nThings get even weirder when we examine the first ICMP packet in the file.\n\n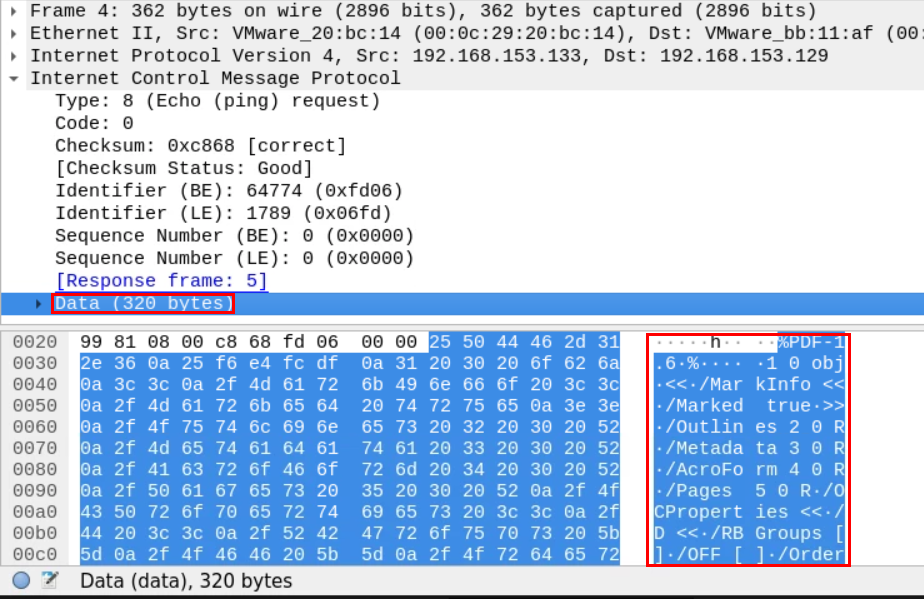\n\nUnlike the normal ICMP ping packets, these seem bigger.\n\nThe Data section seems 10 times larger than the normal, and it contains something familiar.\n\n**%PDF-1.5** is the string we find at the beginning of the PDF files. This looks suspicious.", "solutions_html": "As usual, start by taking a look at the file's statistics is always a good place to begin.
\n
From the protocol hierarchy figure, it seems that HTTP is the protocol which the file we're looking for was downloaded through.
\nIt may be a good idea to look at the HTTP requests made.
\n
Examining the requests made can help us know what type of file we're looking for.
\n
Now we know that it is a PDF file.
\nTo extract the downloaded file, we need to find the network streams which contain that file and extract those bytes into an independent file to open later.
\nOne way to look for the file is using its magic number. Recall how each format has a unique header that can be used to identify that file.
\nWe know from the previous example that the user has downloaded a PDF file from the BBC website using HTTP protocol.
\nWe can use that knowledge to our advantage and look for the PDF signature within the PDF HTTP stream. Using the filter http contains \"PDF\".

After we've found the file and highlighted its bytes, we can use the Wireshark extraction feature to dump those bytes into a separate unique file.
\n
The new file will be saved as a .bin file, all we need to do is to change the extension and open the file with a PDF reader.
\n
Another way to do this would be to export all the objects downloaded through HTTP.
\n
This will give us the list of the objects which we can pick from
\n
After sorting the files at the destination folder, we can examine the extensions and open the files that look interesting to us.
\n
First, let's load the PCAP file located at Desktop/Module7/Lab20/file2.pcap on Wireshark.
\nThe protocol hierarchy for this cap file looks a little different than the other files we examined.
\n
The amount of ICMP traffic within the file is more than normal.
\nThings get even weirder when we examine the first ICMP packet in the file.
\n
Unlike the normal ICMP ping packets, these seem bigger.
\nThe Data section seems 10 times larger than the normal, and it contains something familiar.
\n%PDF-1.5 is the string we find at the beginning of the PDF files. This looks suspicious.
", "flags": [], "min_points_to_pass": null, "access_type": "default", "user_status": "unstarted", "user_lab_status": null, "user_status_modified": null, "user_flags": [], "global_running_session": null }