
You're presented with a capture file which contains encrypted traffic; you need to add the proper certificate using Wireshark and examine the traffic unencrypted.
\nThe certificate can be found at Desktop/Module7/Lab24/certname.pem
\nWhat is the certificate serial number?
\nWho issued that certificate and for whom?
\nWhat is the start and expiration date? What are the used algorithms and key lengths?
\nThe provided PCAP file can be found at Desktop/Module7/Lab24/SSL.pcapng
\nWhat are the ciphers that the client supports?
\nWhat is the suite that the server chose to encrypt the data with?
\nNavigate to Preferences -- Protocols for this task. You can make sure that you added the private key correctly by being able to see some previously unknown SSL packets changing into a known protocol.
\nYou can complete this task by following the streams that were converted to a known protocol.
", "published_date": "2020-10-20T15:32:26Z", "solutions": "# Solutions\n\n## Task 1: Examine The Provided Certificate\n\nWe can examine the certificate with **openssl** using the following command:\n\n```\nopenssl x509 -in certname.pem -text -noout\n```\n\n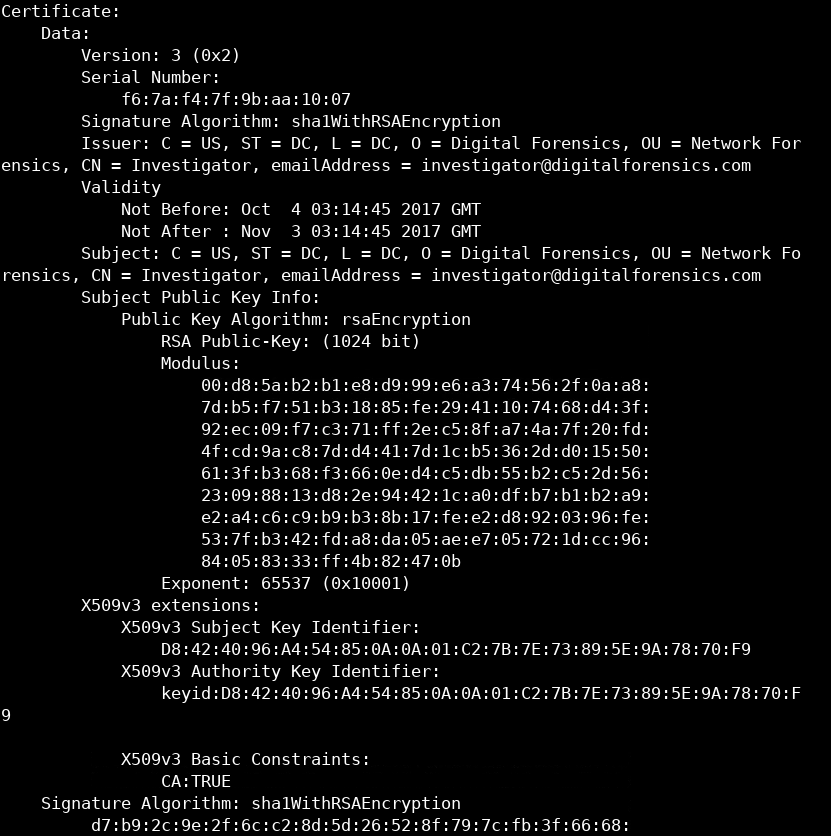\n\nThe Certificate serial number is **f6:7a:f4:7f:9b:aa:10:07.** The signature algorithm is SHA1. The certificate country is the **US,** and the organization name is **Digital Forensics** and issued to **Investigator.** The public key of the RSA algorithm is 1024 bit long.\n\n## Task 2: Examine The First TLS Packet Sent By The Client (the client hello message)\n\nFirst, we need to filter unwanted packets so that we can examine the SSL traffic. We can do that by examining the traffic going to and from TCP port 443 since it is the default port for SSL. Using filter `tcp.port==443`.\n\n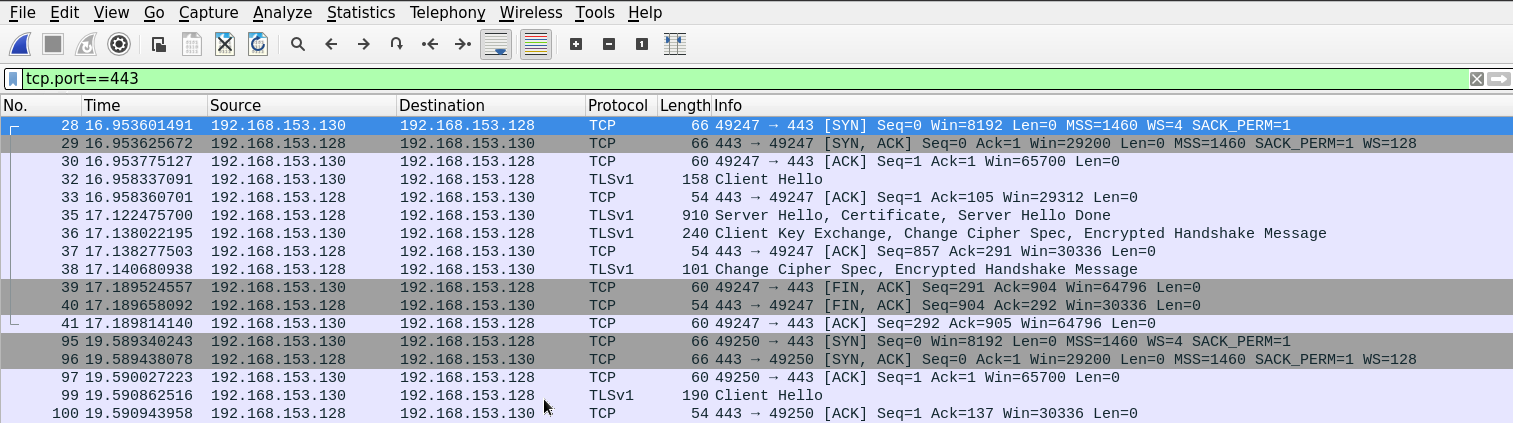\n\nSince the filter we're using displays everything going through 443, Wireshark will also display the three-way-handshake and other TCP segments.\n\nWe can use another way to filter out TCP segments by using the **SSL** filter to display only relevant packets.\n\nThe SSL client hello message can usually be found right after the three-way handshake.\n\nBefore we examine the client hello message, we should notice from the picture above; we can see that there were many attempts to start the SSL session.\n\n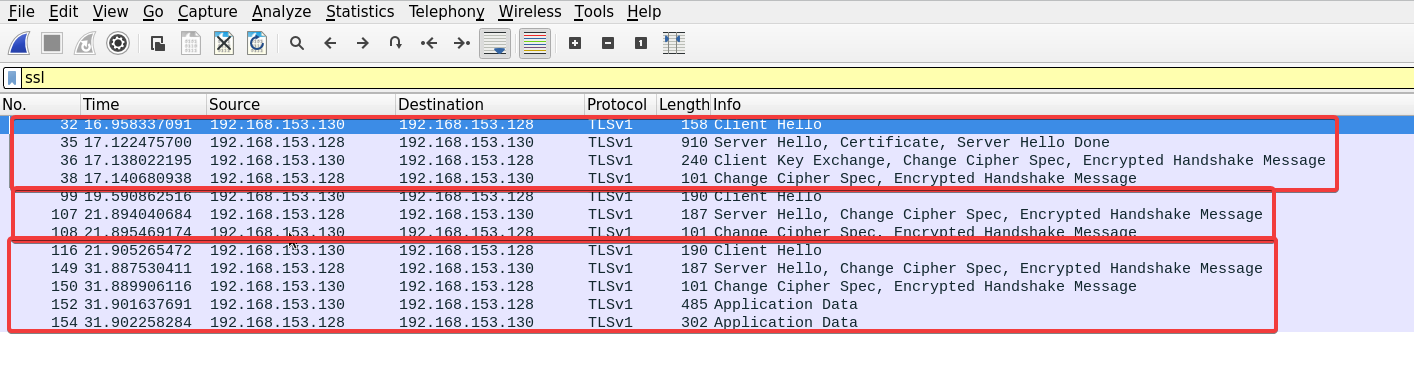\n\nOnly one of those attempts is followed by data exchange.\n\nAfter examining the client hello message of the third connection, we can see the full list of ciphers sent by the clients to the server. Under the *Transport Layer Security* dropdown. \n\n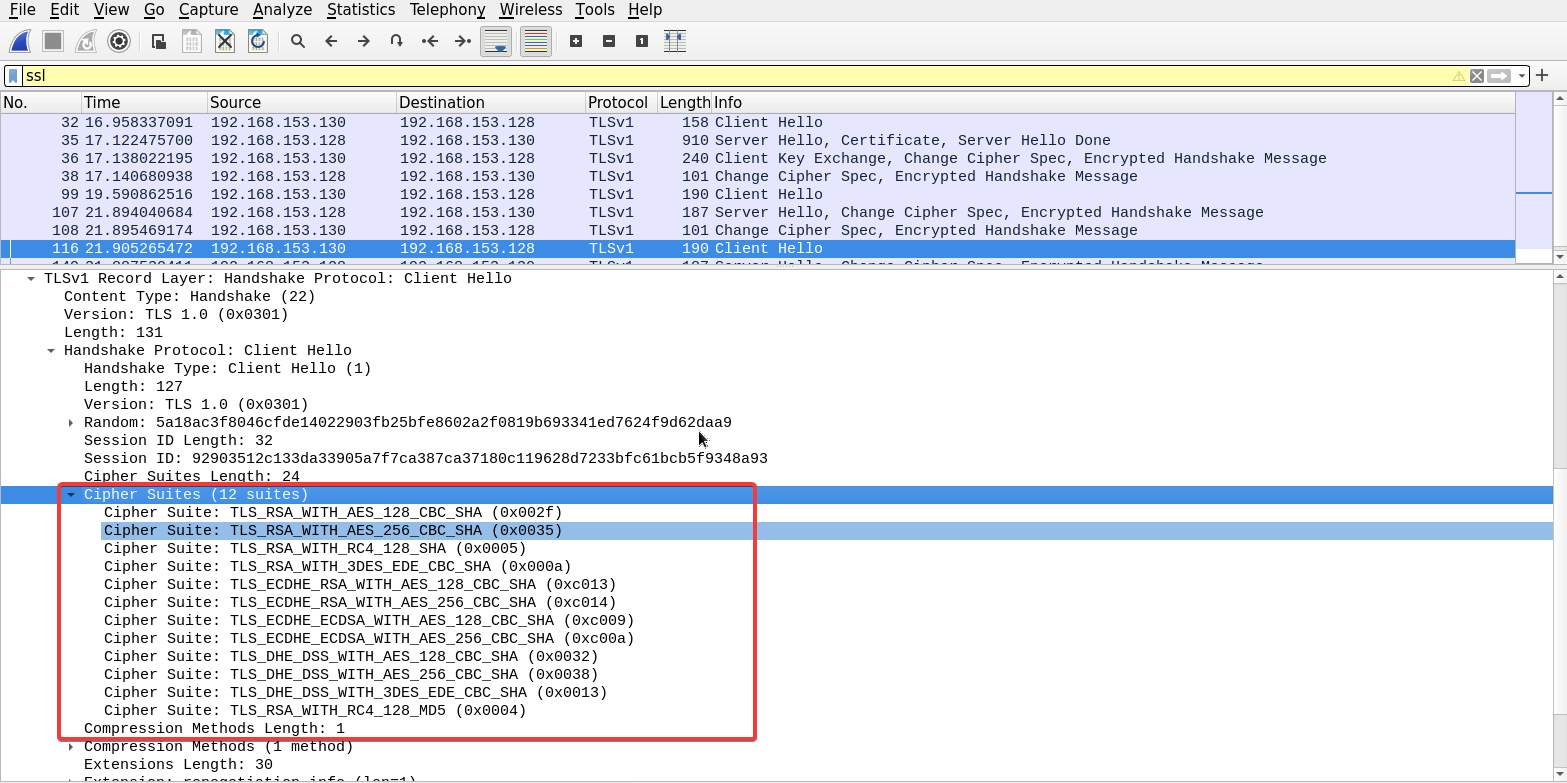\n\n## Task 3: Examine The Server Hello Message\n\nUsing the same method, we can examine the Server hello message to find out which algorithm did the server choose to use to secure the connection.\n\n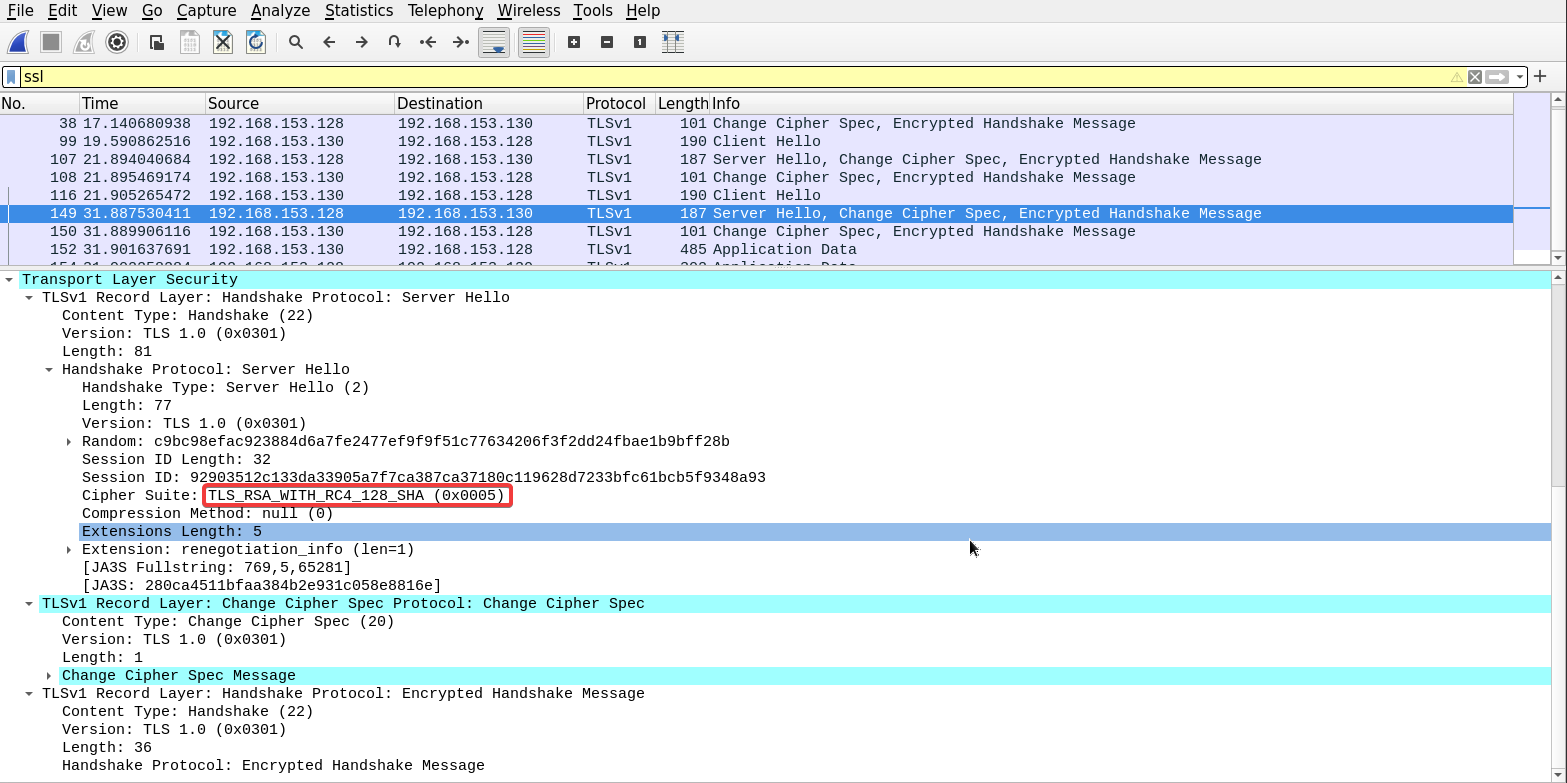\n\n## Task 4: Add The Private Key You Have To Wireshark And Make Sure The Traffic Is Decrypted\n\nFrom the **preference** option under the **edit** tab...\n\n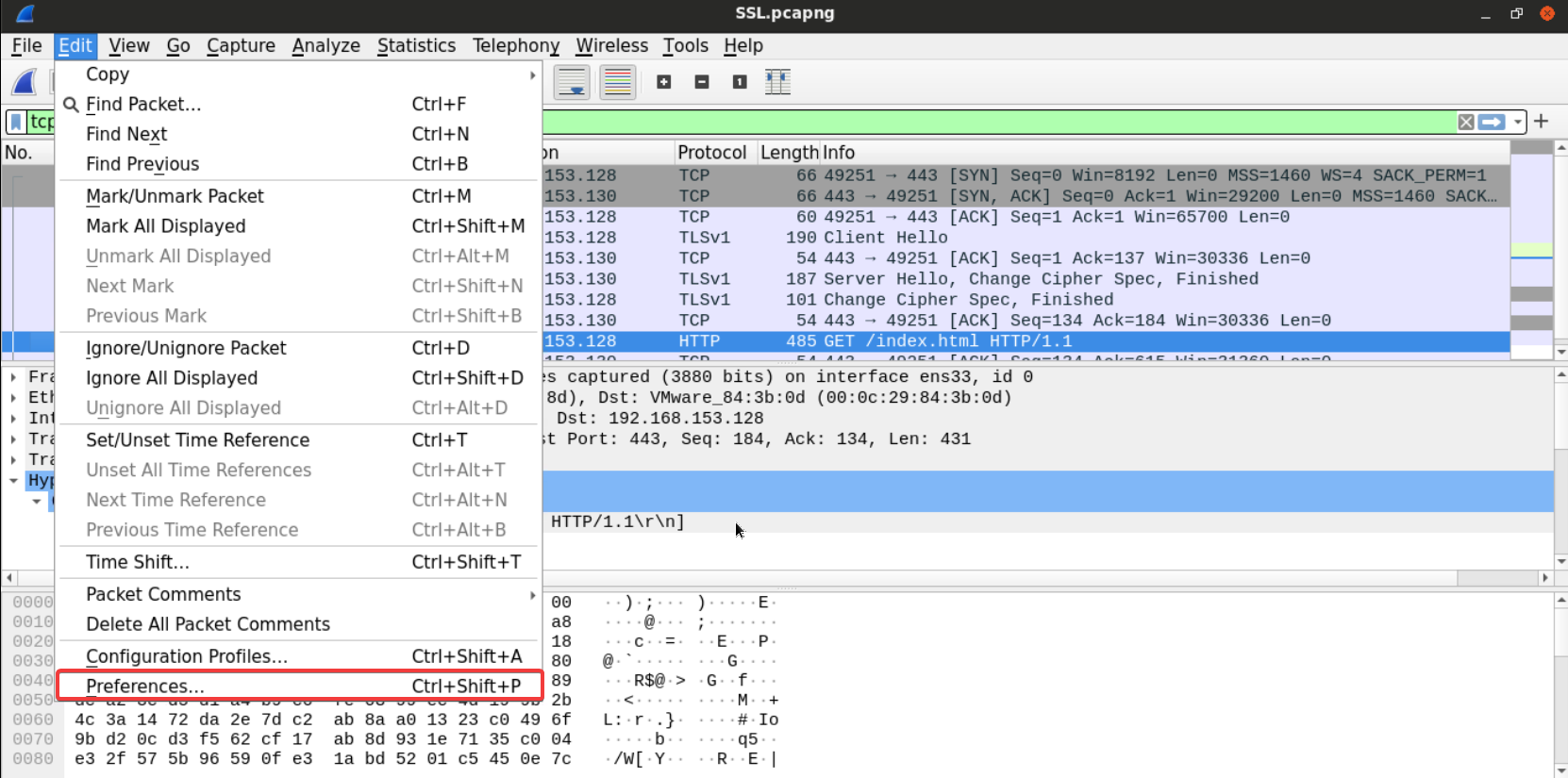\n\nSelect the **TLS** option under the **protocols.**\n\n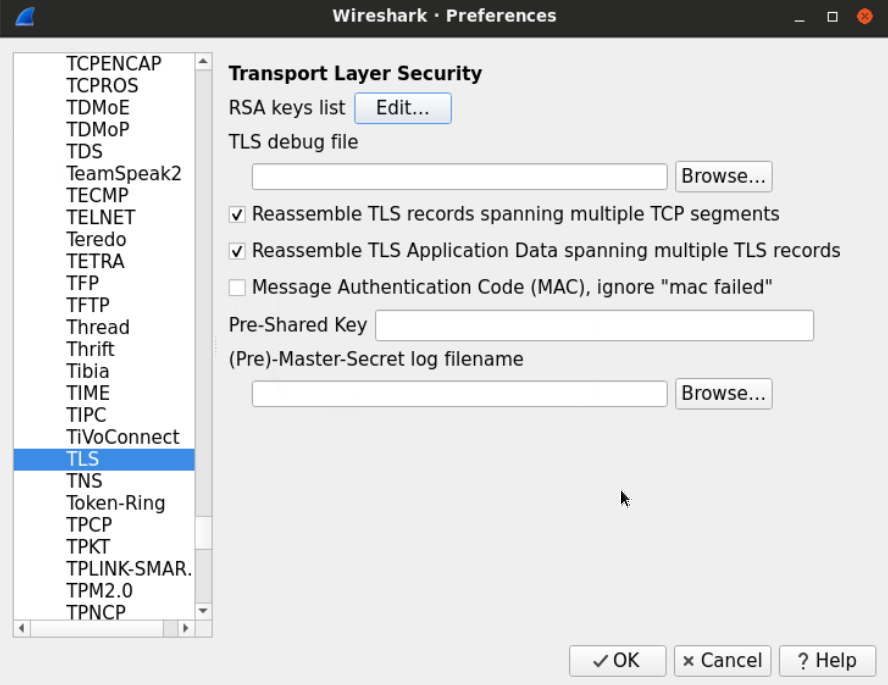\n\nEdit the RSA keys list, and add the private key file named **testkey2.pem,** which can be found at **Desktop/Module7/Lab24/testkey2.pem.**\n\n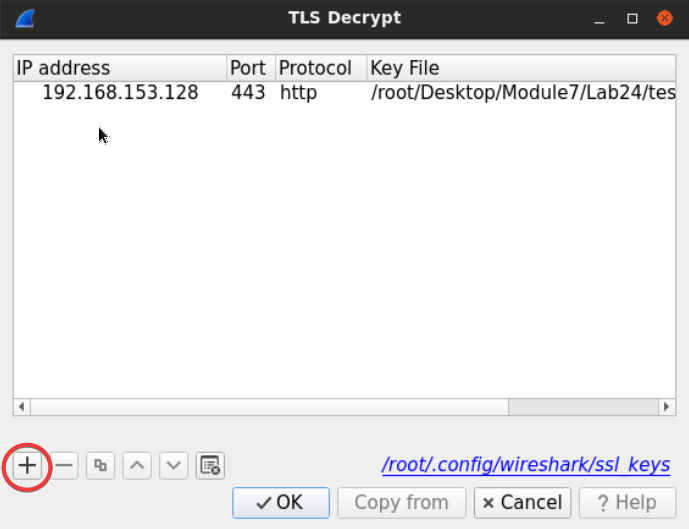\n\nAdd the IP Address of the server, port (443), the protocol we're tunneling (which is HTTP) and the file of the key.\n\n- IP Address: 192.168.153.128\n- Port: 443\n- Protocol: http\n- Key File: test2key.pem\n\n**[Note:]** sometimes you will have to restart Wireshark for this to be effective!\n\nWe can follow the traffic of any TLS connection to make sure the key is working.\n\nAfter adding the RSA key, you'll notice that some packets have changed from unknown SSL packets to some known protocol since the data got decrypted.\n\n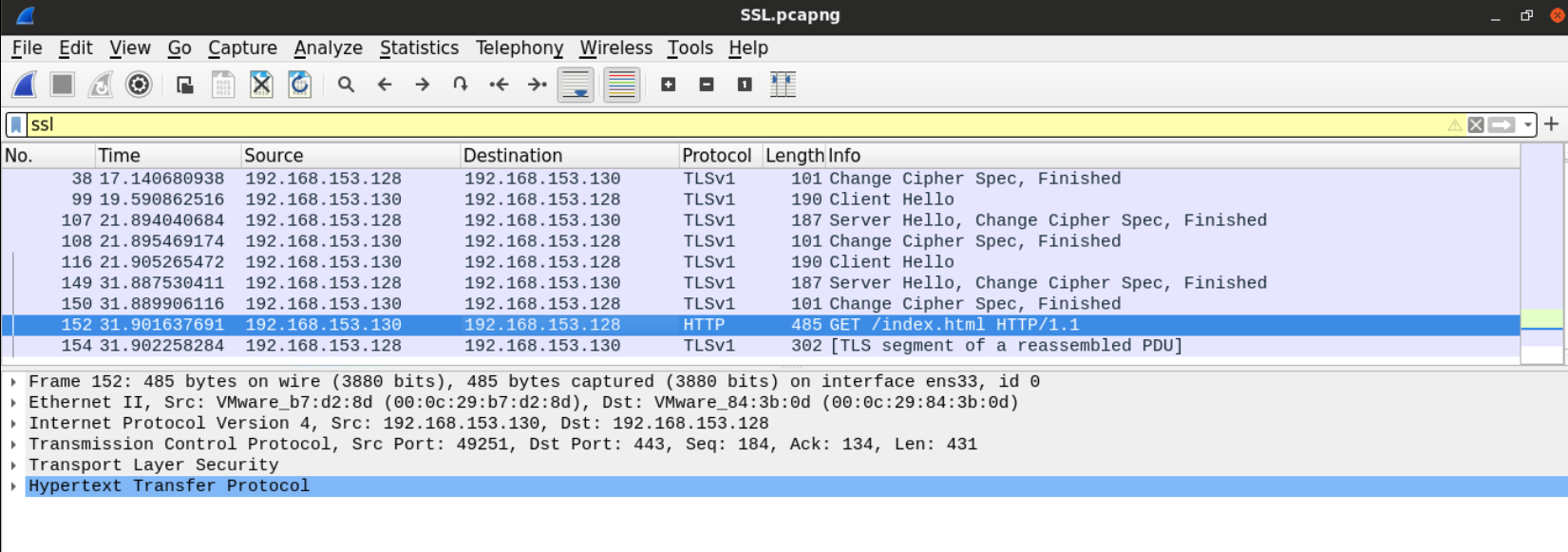\n\n## Task 5: What Is The Content Of The page Which The User Visited Using SSL?\n\nNow that we've decrypted the traffic, we can follow the SSL traffic and see that the client was requesting the serve default index page.\n\n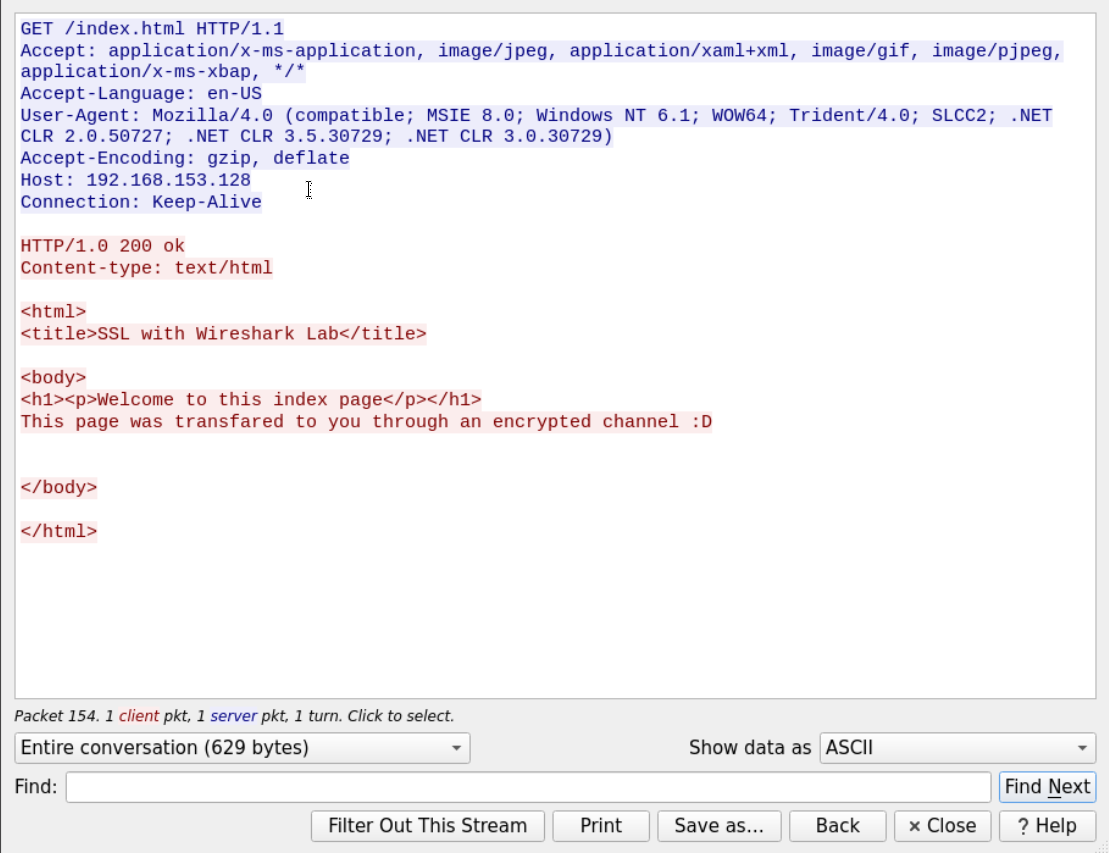", "solutions_html": "We can examine the certificate with openssl using the following command:
\nopenssl x509 -in certname.pem -text -noout
The Certificate serial number is f6:7a:f4:7f:9b:aa:10:07. The signature algorithm is SHA1. The certificate country is the US, and the organization name is Digital Forensics and issued to Investigator. The public key of the RSA algorithm is 1024 bit long.
\nFirst, we need to filter unwanted packets so that we can examine the SSL traffic. We can do that by examining the traffic going to and from TCP port 443 since it is the default port for SSL. Using filter tcp.port==443.

Since the filter we're using displays everything going through 443, Wireshark will also display the three-way-handshake and other TCP segments.
\nWe can use another way to filter out TCP segments by using the SSL filter to display only relevant packets.
\n The SSL client hello message can usually be found right after the three-way handshake.
The SSL client hello message can usually be found right after the three-way handshake.
Before we examine the client hello message, we should notice from the picture above; we can see that there were many attempts to start the SSL session.
\n
Only one of those attempts is followed by data exchange.
\nAfter examining the client hello message of the third connection, we can see the full list of ciphers sent by the clients to the server. Under the Transport Layer Security dropdown.
\n
Using the same method, we can examine the Server hello message to find out which algorithm did the server choose to use to secure the connection.
\n
From the preference option under the edit tab...
\n
Select the TLS option under the protocols.
\n
Edit the RSA keys list, and add the private key file named testkey2.pem, which can be found at Desktop/Module7/Lab24/testkey2.pem.
\n
Add the IP Address of the server, port (443), the protocol we're tunneling (which is HTTP) and the file of the key.
\n[Note:] sometimes you will have to restart Wireshark for this to be effective!
\nWe can follow the traffic of any TLS connection to make sure the key is working.
\nAfter adding the RSA key, you'll notice that some packets have changed from unknown SSL packets to some known protocol since the data got decrypted.
\n
Now that we've decrypted the traffic, we can follow the SSL traffic and see that the client was requesting the serve default index page.
\n